PI: Benjamin Livshits, Imperial College London, Co-I: Alastair Donaldson, Imperial College London, Google
- Web browsers are among the most critical infrastructure on which society depends.
- Testing web browsers to find semantic defects is fundamentally challenging.
- We have employed mutation-based structural fuzzing to help address this problem, focussing on testing WebGL implementations inside major web browsers.
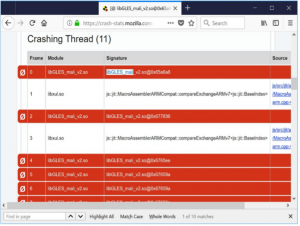
The research work undertaken on this project at Imperial College London led to the development of an automated approach to finding defects in web browsers using mutation-based structural fuzz testing. The investigators decided to focus on testing components of web browsers related to high-performance graphics processing via the WebGL API, because the interaction between web browsers and graphics processing units has become a prominent attack surface in recent years. Two complementary approaches were explored: applying semantics-preserving transformations to WebGL pages to detect rendering problems, where a semantics-preserving change (which, by definition, should have no impact) leads to a change in what is rendered, and applying semantics-changing mutations to a well-formed page in order to test the browser’s robustness to adversarial inputs. This led to the discovery and reporting of a number of issues in the Firefox and Chrome browsers, triggered by underlying defects in GPU drivers from a range of vendors. The associated tool in which the techniques are implemented will be open sourced in due course.
The funding from VeTTS was incredibly useful in allowing us to explore this emerging area.
The line of work started by GraphicsFuzz has led to a series of papers on the reliability of graphics compilers, detailed below and has put us in a good position to apply for follow-on projects – a research grant from the Google Chrome University Research Program has already been secured (more details below). The work is strongly related to a line of work Donaldson has been pursuing for several years on metamorphic testing for graphics compilers, which led to the GraphicsFuzz start-up company that was acquired by Google and has since been open-sourced.
The VeTTS work on fuzzing WebGL has been integrated into GraphicsFuzz, which is actively being used to find defects in the Chrome web browser, including the vulnerabilities linked to below, which have all now been fixed (link)
PUBLICATIONS. [1] “Putting Randomized Compiler Testing into Production (Experience Report).” Alastair F. Donaldson, Hugues Evrard, Paul Thomson, ECOOP 2020. [2] Alastair F. Donaldson, Ben Clayton, Ryan Harrison, Hasan Mohsin, David Neto, Vasyl Teliman, Hana Watson: Industrial Deployment of Compiler Fuzzing Techniques for Two GPU Shading Languages. IEEE International Conference on Software Testing, Verification and Validation (ICST’23) [3] Vasileios Klimis, Jack Clark, Alan Baker, David Neto, John Wickerson, Alastair F. Donaldson: Taking Back Control in an Intermediate Representation for GPU Computing. Proc. ACM Program. Lang. 7(POPL): 1740-1769 (2023) [4] Alastair F. Donaldson, Paul Thomson, Vasyl Teliman, Stefano Milizia, André Perez Maselco, Antoni Karpinski: Test-case reduction and deduplication almost for free with transformation-based compiler testing. PLDI 2021: 1017-1032
RELATED GRANTS. Dr A. Donaldson, EPSRC Fellowship “Reliable Many-Core Programming”, 10/2016-09/2021, £1M. Dr A. Donaldson (Co-I), with C. Cadar (PI), EPSRC Grant “Automatically Detecting and Surviving Exploitable Compiler Bugs”, 01/2018-12/2020, £672K. Dr A. Donaldson, Google Chrome University Research Program project “Automatic Detection of Rendering-Related Security Vulnerabilities in Web Browsers”, 01/2018-04/2019, £130K.
IMPACT. “From a technical standpoint, the GraphicsFuzz work to which this VeTTS project is closely related has been highly successful in developing basic technologies for improving the security and reliability of billions of deployed mobile devices. From a broader point of view, this work has gotten widespread visibility and, of course, was seen by Google as being so valuable that they bought it.” – John Regehr, Professor, University of Utah –